Difference between revisions of "Oauth"
| (5 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
| + | [[Category:OAuth]] | ||
[[Category:API]] | [[Category:API]] | ||
[[Category:Web Services]] | [[Category:Web Services]] | ||
| − | + | Allows an application to access specific resources on behalf of a user | |
| + | <div style="float:right;">__TOC__</div> | ||
[https://knpuniversity.com/screencast/oauth/intro#play https://knpuniversity.com/screencast/oauth/intro#play] | [https://knpuniversity.com/screencast/oauth/intro#play https://knpuniversity.com/screencast/oauth/intro#play] | ||
| Line 99: | Line 101: | ||
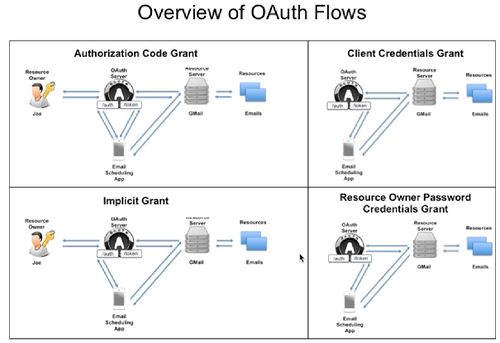
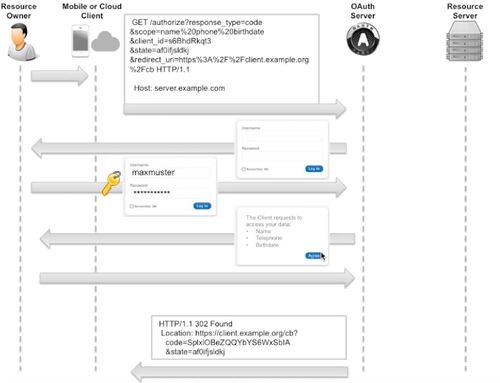
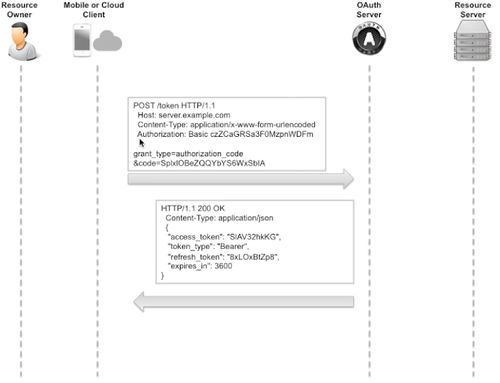
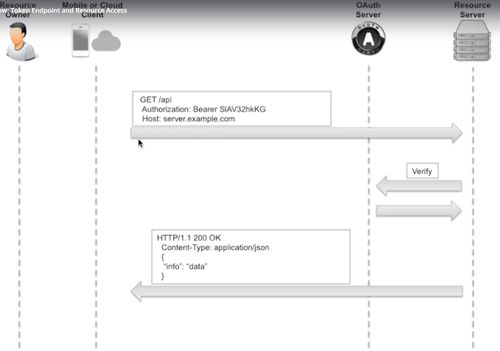
== OAuth Flow == | == OAuth Flow == | ||
[https://www.udemy.com/learn-oauth-2/learn/v4/t/lecture/3285520?start=0 Udemy Lesson] | [https://www.udemy.com/learn-oauth-2/learn/v4/t/lecture/3285520?start=0 Udemy Lesson] | ||
| + | |||
| + | [[File:OauthFlows.jpg|500px]] | ||
| + | --------------- | ||
| + | [[File:OAUTH Flow 1.jpg|500px]] | ||
| + | |||
| + | [[File:OAUTH_Flow_2.jpg|500px]] | ||
| + | |||
| + | [[File:OAUTH_Flow_3.jpg|500px]] | ||
Latest revision as of 09:26, 26 November 2025
Allows an application to access specific resources on behalf of a user
https://knpuniversity.com/screencast/oauth/intro#play
OAuth Actors
OAuth Provider
Based on 3 components
Authentication Provider
Username and Password
Consent Server
Which parts of system a client can access
Token Management Infrastructure
it keeps data like : Access token, refresh token, when it was created and when it's invalid, when it's revoked
Resource Provider
Makes a protected resource available via HTTP Protocol
ie : Twitter
Resource Server
- Holds Resources
- Protects resources
- Makes resources available via API
Resource Owner
Owner of the protected resource.
- Owns resources
- Delegates right to access the resource to a third party app
ie : @aliiybar
Client
An application trying to access a protedted resource.
- Wants to access resources
- Gets and holds Access Token and Refresh Token
- Should NOT hold password of Resource Owner
- Identified via ClientID and Client Secret
ie : Mobile app
OAuth Server - Endpoints
/authorize GET
Input Query Parameters
- state
- scope
- response_type
- client_id
- redirect_uri
Output
according to response_type the output is one of the items below
- Authorization Code (for Authorization Code Grant)
- Access Token (for Implicit Grant)
/token POST
Authorization : Basic clientId:clientSecret
Input Query Parameters
- grant_type
- code
- client_id
- redirect_uri
Output
- Access Token and Refresh Token (for)
- Authorization Code Grant,
- Client Credentials Grant and
- Resource Owner Password Credentials Grant
/verify - not standardized
only internally accessible by Resource Server
Client - Redirect Endpoints
Redirect URI (GET)
Input Query Parameter
- state
- scopes
- code
Resource Server - Resource Endpoint
/api Authorisation : Bearer {Access Token}
Access Token and Refresh Token (for Authorization Code Grant, Client Credentials Grant and Resource Owner Password Credentials Grant)
Tokens
- Access Token
- Refresh Token (it's only for getting a new Access Token, cannot be used to access resources)
- Authorisation Code it's valid for just few minutes. It's for getting Access Token. It can only be processed by OAuth Server it will never be sent to resource provider
Credentials
- Resource Owner Credentials
- Client Credentials : ClientID & ClientSecret
- Access Token
- Refresh Token
- Authorisation Code
Client Registration
- With OAuth Provider
- Client porvides to OAuth Provider
- Redirect URI
- Required Scopes
- Client obtains from OAuth Provider
- ClientID
- ClientSecret